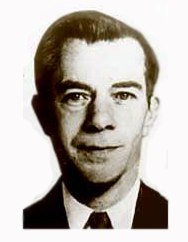
Is bank robber Willie Sutton the inspiration of cyber criminals who are targeting small businesses?
If you thought only big business and infrastructure were at risk from cyber terrorism and cyber criminals, think again.
Small and medium-sized businesses are the new favorite targets of cyber criminals. This is according to Verizon’s 2011 Data Breach Investigations Report. That makes it something that affects every company of every size. It causes destruction and disruption and it has to be stopped.
Why Cyber Criminals Pick on Small Businesses
According to the Verizon Report the reasons are: “hackers favor highly automated, repeatable attacks against these more vulnerable targets or possibly because criminals are opting to play it safe in light of recent arrests and prosecutions of high-profile hackers.”
Personally, I think it’s a lesson from the “Willie Sutton Crime School”. As every good bank robber knows, you go where the money and targets are. There are millions more small businesses than large: 5,717,302 (<500 employees with most having less than 20 employees) as compared with 17,236 (500+ employees) according to the SBA.
For smaller businesses, the greatest danger comes from ourselves and from those we trust and rely on, our providers and strategic partners and allies. We can’t fight this alone. We all have to do our part and work together.
What Makes Small Businesses Vulnerable to Cyber Terrorism
Cyber criminals look for vulnerabilities they can exploit. You are at risk if you conduct business. If you:
- Use checks or take checks. Cyber attackers duplicate checks with your routing number and cash them. If they’re your checks, your money vanishes; if you take these fraudulent checks and cash them, you can lose your money, too.
- Use credit cards or take credit cards. Same issues as checks.
- Use software, even software in the cloud. You can open a “back door” to your data and systems that a cyber criminal can use or you can be infected and infect others.
- Use passwords — especially if you use the same ones for everything, don’t change them often enough, make them strong, or protect others from getting access to them.
- Send and receive emails — they can infect you and others as well as cause problems with other systems.
- Have firewalls — some aren’t strong enough or aren’t kept current.
- Put fuel in a vehicle, use an ATM, or have or use any kind of point of sale machine including “self checkout” devices.
Read the recommendations from the Department of Homeland Security of how to address cyber security and it looks like the day the in the life of a business.
Basically, everything you do, say, or write can be hacked, attacked, usurped, used the wrong way, etc. Even your sales profiles. According to Andy Kemshall, technical director of SecurEnvoy, cyber criminals long-term strategy is to create their own profiles to go along with the stolen credentials so they are within norms and don’t raise red flags. This completely counteracts one of the most effective online fraud deterrents available that analyze transaction histories to establish a customer’s basic use profile. When a new transaction is sufficiently outside the norm, the transaction can be subjected to further scrutiny before it’s approved. You think it’s a customer and it’s really a criminal or someone thinks it’s you or your business and it’s not.
In short, “all the technology we’ve created to benefit us,” Lech Janczewski and Andrew Colarik authors of Cyber Warfare & Cyber Terrorism say, “could also be used as a tool of attack/destruction against us.”
Three Effective & Inexpensive Actions Your Business Can Take to Begin to Defeat Cyber Terrorism
Cyber criminals steal a business’ good name and reputation. Just the threat of cyber terrorism makes employees, customers and owners afraid, vulnerable, and less productive. Defeating these business criminals takes three C’s: community, control, and commitment.
These are some simple actions any business can take.
- Start a community. Set up an informal group to talk about the issue. Awareness has to come before action. Keep meeting. Share what you learn and your experiences. Don’t be ashamed. Top cyber experts say there are only two kinds of businesses: those that have been hacked, and those that don’t know they’ve been hacked. As a consumer, you’re part of a third group: those who know they’ve been hacked and won’t admit it.
- Look at your business controls. Have a discussion with all employees about cyber terrorism and get them engaged in prevention and detection. Set up a training program, reward employees for their ideas and efforts. Ask your providers what controls they have to address this threat. You don’t necessarily need proof but you do need to evaluate if they’re doing enough. If not, suggest what would make you less vulnerable. Providers who are disengaged may not be your best choice for products and services for your business.
- Be committed to putting these in place, maintaining them, and changing them. The new approach, according to Eric Savitz at Forbes, is to keep agile and get away from old remedies that are static, set-and-forget. You may have only minutes between entry and compromise. Read and put in place ideas from organizations like the Department of Homeland Security. Bookmark Computer Security Institute which tracks and reports on cyber breaches including conducting the yearly Computer Crime and Security Survey, the longest-running project of its kind in the security industry that reports on information about targeted attacks, incident response and the impacts of both malicious and non-malicious insiders. Use these ideas where appropriate but evaluate and track your efforts. Hold yourself and your employees and your providers accountable for staying ahead when it it comes to cyber security.
The opposite of cyber terrorism is cyber security. Make it one of your top business priorities at all times.
“The power of one, if fearless and focused, is formidable, but the power of many working together is better.” Gloria Macapagal Arroyo
Unleash this power! Here’s to our success!






Leave a Reply
You must be logged in to post a comment.